Advanced Security
We consider physical and logical security within an organization to be a critical consideration in the planning and implementation of infrastructure solutions. For connecting remote points together across a Wide Area Network, encrypted VPN site-to-site tunnels are used to protect data flow. Additional considerations are required for logical security at the primary site to analyze traffic patterns and employ threat detection algorithms. Firewalls on the aggregate layer are designed with permanent static ACLs but also implement dynamic ACLs propagated by border IDS automation. Application layer protection is also implemented using proxies between the border and internal application servers for specific protocol filtering, with suspicious states being marked and tagged upstream for elevated IDS awareness.
- Encrypted site-to-site VPN for remote branch communication
- Border IDS analyzing traffic flow and identifying threats
- Aggregate firewalls utilizing dynamic ACLs from IDS propagation
- Application layer protection by implementing filtering proxies
Logical Diagram
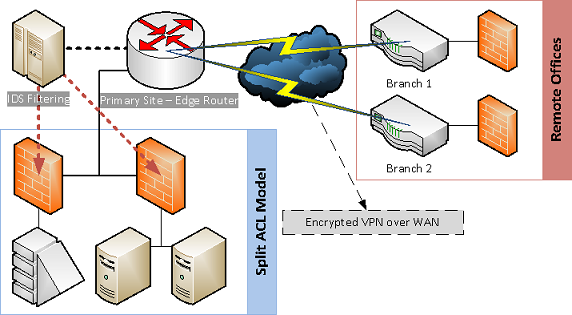
- Encrypted VPN tunnels over WAN circuits to remote branches
- Split ACL model to separate internal security zone areas
- Border IDS monitoring for active threat and risk detection
- ACL propagation from border IDS to aggregate firewalls
Encryption
A strong consideration for advanced security design includes the use of encryption services to protect critical data. We employ the use of encryption services both within network layer and local layer infrastructure to offer protection against remote and local threats. Deployments requiring frequent data replication across multiple geographic locations would benefit from encrypted tunnels across MPLS/VPLS circuits where edge security appliances are placed at each point. When working with remote devices which cannot be covered under traditional physical security standards, we mitigate risk by securing locally stored data with powerful encryption and multi-factor authentication systems.
Altexxa Group believes strongly in encryption services to protect all corporate data traveling over wide area networks, while also ensuring local security considerations are met. Encryption and multi-factor authentication systems provide protection for organizations and critical data.
- Protection against both remote and local threats
- Wide area network protection with encrypted tunnels
- Remote devices utilizing encrypted storage and MFA
Intrusion Prevention
A key component in a high security model is the intrusion prevention layer. An IPS will provide filtering for known attack patterns and also enforce ACLs. In a high security model, the IPS will also be driven by a border IDS employing advanced algorithms for threat detection. Heavy importance is also placed on strong ACLs to ensure applications are protected from unauthorized users. This can be achieved with a split ACL model and division of security levels across separate network segments.
Altexxa Group works primarily with Sophos UTM and Cisco ASA deployments, with custom designed BSD based border threat detection systems. Our border IDS performs fast assessment and intelligent flagging for undetermined anomalies to further investigate patterns.
- Enforcing ACLs and filtering known attack patterns
- Automated orchestrator combining border IDS and IPS
- Border assessment and intelligent anomaly flagging
Deployment
Advanced security implementation at the primary site utilizes a split ACL model which segregates network layers based on access requirements. In addition to ACLs and IPS within the firewall appliances, edge border filtering is added to detect traffic anomalies. Altexxa Group uses a BSD based filtering solution at the border which ties in with our standard aggregate layer protection. Communication over WAN with remote branches is done with site-to-site encrypted VPN tunnels between edge firewall appliances with ACL considerations to protect primary site assets. Additional protection utilizing data encryption methods can be implemented for remote devices to mitigate theft risk. We employ the use of multi-factor authentication combined with profile driven ACLs to ensure data integrity.
- Network layer segregation based on access requirements
- Border IDS filtering working with aggregate layer firewalls
- Remote WAN connectivity utilizing encrypted VPN tunnels
- Multi-factor authentication and profile driven ACLs