Disaster Mitigation
Disaster mitigation and recovery scenarios will frequently include geographical risk considerations, though additional design factors should also include logical risk evaluation for protection against direct data threats. By reviewing cost-benefit analysis, we can determine the required disaster mitigation design structure needed to protect critical applications and organization data. Standard mitigation and recovery policies include local High Availability implementation with critical data replicated to off-site locations. Creating a mitigation policy functioning under a "never down" model requires a secondary site and additional networking considerations due to bandwidth and routing needs. The use of multi-site replication should follow diverse geographical planning and network path evaluation.
- Risk considerations include geographical and logical factors
- Policy structure design determined by cost-benefit analysis
- Off-site data replication for critical organization data
- Bandwidth and routing requirements for hot-site implementation
- Risk evaluation with geographical and network path considerations
Logical Design
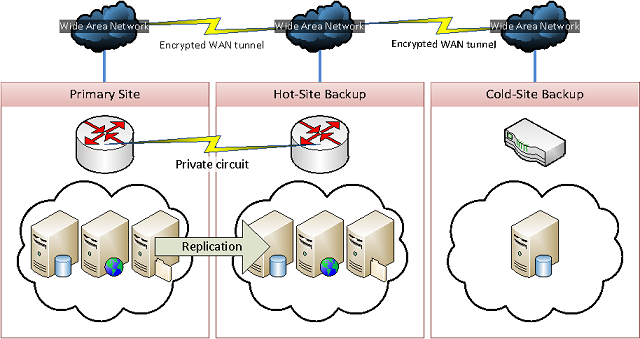
- Primary to hot-site replication over dedicated private circuit
- Cold-site backup for critical organization data via encrypted tunnels
Evaluating Risks
We divide risk considerations into two separate classifications consisting of direct and indirect threats. A risk falling under the direct threat classification will generally involve disaster causes by means of natural factors whereas indirect threats account for human factors.
Direct threats to infrastructure include natural disasters such as earthquakes or floods, and must remain a critical component of risk evaluation when reviewing geographical components of a deployment design. Infrastructure designs in high risk areas should incorporate additional redundancy components to assist with mitigating disaster.
Indirect threats to infrastructure include certain risks which may not be predictable using standard risk assessment. Risks under this classification may include political and economical challenges.
- Establishing classifications based on risk nature
- Infrastructure design risk considerations
Implementation
The disaster mitigation plan implementation will rely on the classifications and risk zones per our risk assessment. A standard implementation will require a minimum of one hot site connected to the primary site over geographically redundant network backbones for data replication. Implementation within high risk zones will include either one additional hot site or a cold site backup designed to act only as critical data storage should the primary and hot site become compromised.
Our plan implementation will also involve network considerations at hot spare sites to account for routing advertisements in the event of primary site failure. We work with network upsteam providers to ensure the necessary policies are in place to establish connectivity at hot sites during a failover action.
- Creating hot/cold sites based on risk evaluation
- Replicate critical enterprise data beyond risk zones
- Working with network providers for transparent routing changes