Load Balancing
For application distribution supporting a large number of external users and following a High Availability model, the deployment of load balancing solutions is critical to ensuring capacity requirements are met. The implementation of a load balancing solution works within the High Availability model by polling health status of assigned node clusters and directing connections around dropped hosts. This solution also allows for scalable application infrastructure as additional capacity can be added within existing clusters when required. Logical deployment involves the redundancy model where balancing units are paired in a failover configuration to protect application uptime.
- Meeting capacity requirements for application distribution
- High Availability model for backend node cluster health
- Scalable application infrastructure for addressing growth
- Follows redundancy model by utilizing hardware failover
Logical Diagram
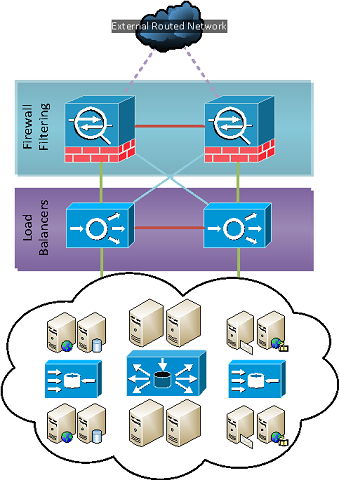
- Firewall and load balancers in High Availability configuration
- Distributed load across multiple backend services
Deployment
Our standard deployment scenario requires compatibility within High Availability and redundant infrastructure models. Other deployment factors considered during design include vendor selection and security layer availability. Altexxa Group works primarily with the Sophos UTM as an integrated solution offering both the security layer and the load balancing solution within one package. We also work with Cisco specific deployments which utilize a combination of ASA/ACE and backend content management engines. Following the mirror deployment layout under our redundancy model, we utilize High Availability pairs to manage failover requirements for load balancer systems and additional units functioning as the separate security layer. This also requires multiple network paths to internal node clusters as we must eliminate single points of failure under the redundancy model.
- High Availability and redundant infrastructure model compatibility
- Vendor considerations for integrated or segregated security layer
- Mirror deployment structure for working within redundancy model
- Network path considerations to eliminate single points of failure
Considerations
Deployment considerations for load balanced environments will include application layer review to determine required protocols as well as security ACL implementation. Standard deployments will often include HTTP/HTTPS balancing across internal clusters and the use of proxy caching services. Requirements for additional protocols such as mail services and user protocols (telecommunications, peer-to-peer) may involve additional balancing outside standard deployed infrastructure. Security considerations should also include network segregation between security ACLs ensuring infrastructure division to provide logical application protection. Further network layer considerations may be involved for distributed content deployments where geographical implications require shortest path content delivery. Diverse protocol and security needs will require vendor selection review to determine deployment needs for load balancing infrastructure.
- Application layer protocol and security ACL requirements
- Standard HTTP/HTTPS proxy services and user protocol support
- Network segregation in high security design model for logical protection
- Distributed content systems requiring advanced network implications